SUPPLY CHAIN
By John W. Spink, Ph.D., Assistant Professor, Department of Supply Chain Management, Business College, Michigan State University and Director, Food Fraud Prevention Academy; and Roy Fenoff, Ph.D., Associate Professor, Department of Criminal Justice, The Citadel and Forensic Document Examiner
Food Fraud Prevention Meets Supply Chain Digitalization: Why Old Systems are Not Enough
The intersection of digitalization, omnichannel operations, and automation is creating both challenges and opportunities for food fraud prevention

Image credit: gorodenkoff/iStock/Getty Images Plus via Getty Images
SCROLL DOWN
A digital transformation that is supposed to make a supply chain more transparent might actually be making it more vulnerable to fraud. Companies are connecting everything—warehouses, suppliers, distributors, retailers—without asking a crucial question: Who is checking the products, information, and documents flowing through all of those connections?
Industry is in the middle of a massive shift. Supply chains are going digital, omnichannel operations are becoming the norm, and automation is everywhere. This should be good news for food fraud prevention. More data should mean more visibility, but in reality, it also creates more opportunities for both prevention and exploitation.
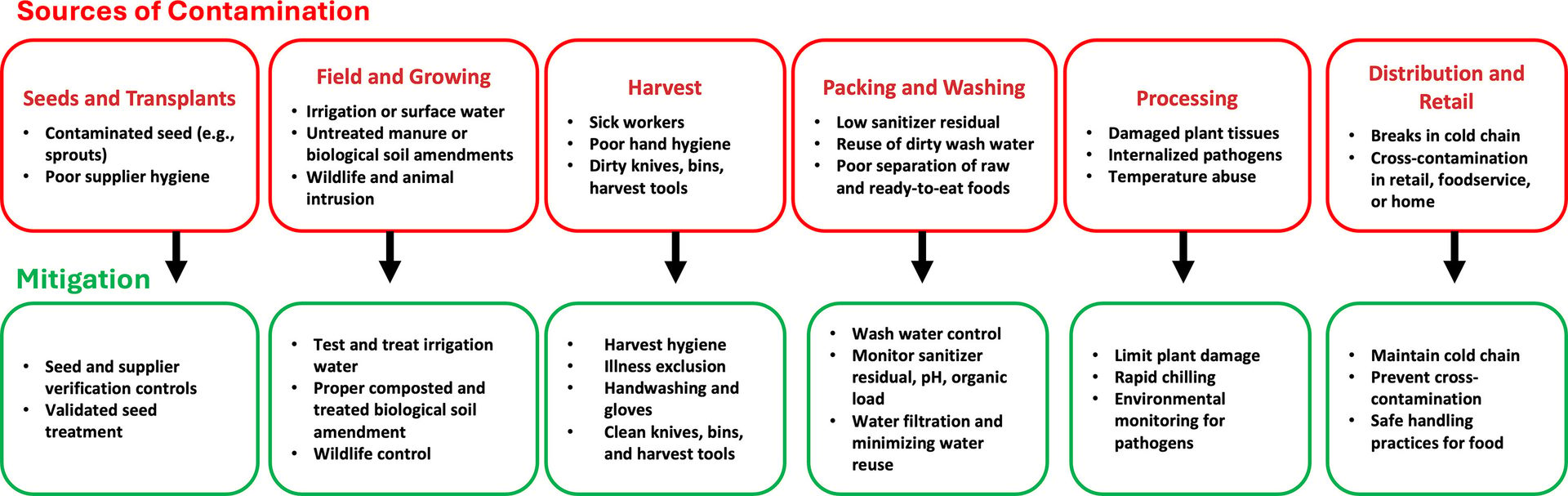
FIGURE 1. Sources of Pathogen Contamination and Methods of Mitigation (Credit: A. Abdelhamid)
Our Experience: Why This Matters Now
Over the past several years, the authors have presented on food fraud prevention and supply chain vulnerabilities to organizations worldwide including INTERPOL, global food companies, and regulatory agencies. Dr. John W. Spink, a professor in Michigan State University's Department of Supply Chain Management within the Business College, is one of the most widely published researchers in food fraud prevention. Dr. Roy Fenoff is a professor of criminology at The Citadel and a forensic document examiner with expertise in fraud and broader crime prevention strategies. This diverse expertise is a rare multidisciplinary combination for food industry applications and scholarly works. Together, we have seen how digital transformation is reshaping both fraud opportunities and prevention strategies.
Supply Chain Digitalization: The Double-Edged Sword
What does digitalization really mean? It is not just about having computers; it is about creating digital warehouses, data lakes, data oceans, and connected systems where information flows seamlessly from farm to fork. Everything is supposed to talk to everything else.
The promise is complete visibility, real-time tracking, instant alerts, and near-perfect traceability. It sounds like a food fraud prevention dream, but here is the hidden part: virtually every known food fraud incident has included fake or manipulated documentation somewhere in the supply chain. Those documents contained information in digital format, such as certificates of analysis, organic certifications, country of origin declarations, and even simple measures such as the weight of a shipment. These documents may have included test results or supplier approvals, with much of this information being digitized.
Fraudsters are not avoiding digital systems; in fact, they may be exploiting them. Consider the example of a mid-sized food manufacturer that digitized its supplier onboarding and compliance documentation to improve efficiency. A supplier uploaded a certificate of analysis (COA) for a high-risk ingredient that appeared complete and valid. The document passed automated checks because it existed, was formatted correctly, and came from an approved supplier account. Over time, that same COA was reused across multiple shipments and automatically pulled into purchasing, quality, and audit systems. Months later, a regulatory inquiry revealed that the laboratory listed on the COA had never performed the testing. The document had been altered once, uploaded into the system, and then replicated flawlessly through digital workflows. No alarms were triggered—not because controls failed, but because authenticity was never part of the control design.
When systems are connected without managing document authenticity, it essentially builds a highway system for fraud. A fake certificate uploaded in one location can flow through an entire network before anyone questions it. If a fraudulent document is in a system, then a security feature such as a blockchain could lead to overconfidence and additional vulnerability. An altered test result can trigger automated purchasing decisions. A counterfeit organic certification can make it into a company's supplier database and stay there for years.
The challenge is not the technology itself. Digital systems can be incredibly powerful tools for fraud prevention. The problem is that most companies implement digitalization for efficiency and cost savings, not for security—essentially building the infrastructure without building the controls.
Omnichannel Everything: More Touchpoints, More Vulnerabilities
The food industry is undergoing another transformation: omnichannel operations. Consumers want to shop anywhere, anytime, and receive products from wherever is most convenient. They want to be able to order online and pick up in-store, or browse in-store and ship from a regional warehouse. They want to be able to subscribe for weekly delivery direct from a supplier.
This is great for customer experience, but it is challenging for supply chain management. It can also cause headaches for food fraud prevention if the proper guardrails are not in place. The reason is that omnichannel operations multiply touchpoints. Products can ship from local retailers, mini-warehouses, major distribution centers, or directly from suppliers. Each channel has its own documentation flow. Each touchpoint is a potential vulnerability. Each fulfillment option adds new suppliers, routes, documentation flows, and personnel handling sensitive information. When those documents are not verified the same way at every location, it can cause problems.
An informal approach to supplier management does not scale in an omnichannel world. A business might know its core suppliers well, but it may not be as familiar with the regional distributor who now ships directly to customers or the third-party logistics provider managing a mini-warehouse across the country. Similar murkiness is seen with "gig economy"-based third-party delivery services. This is where supply chain mapping becomes critical—as discussed in more depth later in the article.
Automation and Data: The Scale Challenge
Adding automation into this mix further complicates the story. Examples include automated ordering, approvals, invoice processing, compliance checks, and even advanced technologies like artificial intelligence (AI) and large language models. Automation is essential when handling massive data sets from numerous sources. No human can manually review every document, every transaction, and every data point flowing through a modern supply chain; the volume is simply too large.
Automation executes what it is programmed to do, and herein lies the problem. If a system is programmed to check that a certificate of analysis "exists," then it will confirm existence, not authenticity. It will not flag subtle inconsistencies or question whether the document matches the product.

“When documents are fraudulent, everything downstream is compromised, regardless of how sophisticated a company's testing protocols or supplier audits might be.”
The good news is that automation can also be an excellent defense when it is set up correctly. With more digitalization, more information can be tracked, patterns can be identified, and anomalies can be flagged that would be impossible to catch manually. Documents can be monitored at scale, information can be cross-referenced across systems, and inconsistencies can be detected in real time. These errors and inconsistencies can be caught, but only if systems are designed to manage food document fraud, not just process paperwork.
Food Document Fraud: The Missing Piece
Food document fraud management is a critical gap in most food fraud prevention strategies. Food document fraud—which we conceptualize using the ISO 22380:2018 document security framework1—is crucial to understand, as it helps industry stakeholders recognize and prevent deceptive practices, fostering trust and clarity in food transactions.
Documents are the connective tissue of a supply chain. They authenticate products, certify compliance, establish traceability, and enable transactions. When documents are fraudulent, everything downstream is compromised, regardless of how sophisticated a company's testing protocols or supplier audits might be. In digital supply chains, the risk is not only that fraudulent documents spread quickly, but also that they become embedded as trusted master data. Once accepted, they can be reused across multiple systems, lots, and decisions without further scrutiny.
Most companies focus on product fraud—testing the actual food for adulterants, contaminants, or substitutions. This is important. However, if the risk of document fraud is not managed, then the vulnerability that enables product fraud will be missed.
Food document fraud is a distinct challenge that requires specific expertise and dedicated management systems. It is not just IT security or supplier audits; it is understanding how documents flow through a supply chain, where vulnerabilities exist, and how to implement controls that actually work in a digitalized environment.
Note: We will explore food document fraud in depth in an upcoming article, including the five document format types that are important to understand and how to build effective prevention systems.
Supply Chain Mapping: Make it Formal
Supply chain mapping is a formal, documented, system-wide supply chain method of mapping that becomes part of an official risk management process. The authors have found that most companies know their Tier 1 suppliers (who they buy from directly) pretty well. They might have some visibility into Tier 2 (who their Tier 1 suppliers buy from). Beyond that, visibility tends to be limited—which is where the vulnerabilities often hide.
Supply Chain Risk Management (SCRM) is a formal discipline and set of procedures. It is not new. Many supply chain teams likely have systems, processes, and tools for managing disruptions, optimizing costs, ensuring continuity, and even formal compliance requirements. What they might not have is integration with food safety and food fraud prevention efforts.
This is a missed opportunity. Supply chain teams are already mapping suppliers, transportation routes, and distribution networks. They are already identifying choke points and vulnerabilities—just from a different perspective. These teams are thinking about delays, capacity constraints, and cost fluctuations—but they need to think about fraud vulnerabilities, too.
Engaging supply chain team as partners, not just service providers, is key. Use their formal systems, learn what they are already tracking, understand what data they have access to, and then work together to overlay food fraud risk onto their existing SCRM framework. It might be surprising to find out what they know and how they can contribute.
Supply chain mapping for food fraud prevention needs to identify:
- All tiers of suppliers, not just direct relationships
- Geographic risk factors and routes
- Document flows and handoff points
- Where products can enter or exit a controlled supply chain
- Critical control points where authentication matters most.
This is not a one-time exercise. Supply chains are dynamic, and mapping must function as a living system that evolves as suppliers, routes, regulations, and documentation requirements change.

“The goal is not to eliminate all risk, but to reduce vulnerabilities to a level consistent with an organization's risk appetite.”
Formalizing a Food Fraud Prevention Strategy: Three Essential Steps
Companies do not need to start from scratch when tackling these concerns and requirements. They simply need to formalize and update what they may have already started years ago.
Step 1: Conduct a System-Wide Food Fraud Vulnerability Assessment—Again
Most companies completed a food fraud vulnerability assessment years ago to meet GFSI requirements. That might have been in 2018, 2019, or 2020 for some. Since then, many companies have focused on incremental updates. However, operating models have changed. Suppliers, routes, distribution channels, and digital workflows look very different today, as does the fraud landscape.
A vulnerability assessment conducted five or seven years ago is now out of date. It does not account for omnichannel operations or reflect the use of digitalized systems. For many companies, it may not cover all of their current suppliers. Generally, it is a good management practice to take the time to reassess everything from the top down—and bottom up—every so often. Now is a good time to do that—not just because it is a requirement for GFSI-related food safety management system compliance, but because it is the only way to know where actual vulnerabilities exist.
A current assessment must reflect omnichannel operations, automated systems, document flows, and indirect suppliers. It should be comprehensive, integrated into regular risk cycles, and reviewed whenever major changes occur.
Step 2: Integrate with the Enterprise Risk Management System
Food fraud prevention cannot exist in isolation. It needs to connect with a company's overall risk management framework—i.e., Enterprise Risk Management (ERM).
U.S.-based public companies are required by the Sarbanes-Oxley Act2 to have an ERM system. Even if a company is private, its owners or investors probably expect to have something similar in place. These systems exist to identify, assess, and manage risks across the entire organization.
Food fraud is an enterprise risk. It can trigger recalls, damage brand reputation, result in regulatory action, and destroy shareholder value. It belongs in the ERM framework, not just in the food safety domain. This integration does two important things:
- First, food fraud risk can be quantified in business terms that the CFO and Board understand—e.g., actual financial exposure, likelihood assessments, and risk rankings that can be compared against other enterprise risks.
- Second, it connects a food fraud prevention strategy with corporate resource allocation decisions. When it can be shown that document fraud vulnerabilities exceed a company's appetite for risk—using the same framework and language that the company's executives use for all other risks—it is much more likely that resources will be allocated for food fraud prevention.
This is where formal supply chain risk management systems become essential. The supply chain team already speaks the language of enterprise risk, and they already have processes for escalating issues to executive leadership. This existing infrastructure should be utilized.
Step 3: Answer the "How Much is Enough?" Question
This is the most challenging question in food fraud prevention: How much risk or vulnerability is simply too high, and how can it be determined when the risk is reduced to an acceptable level? This is often followed by a broad, practical question: How much time, money, and effort should really be invested in that reduction?
The answer is not "as much as possible" or "whatever it takes." That is not realistic, and it is not how business decisions are made. The goal is not to eliminate all risk, but to reduce vulnerabilities to a level consistent with an organization's risk appetite. So, the answer is: Enough to bring a company's vulnerabilities within its risk appetite.
This is where Enterprise Risk Management thinking becomes practical. Every company has a defined risk appetite—i.e., the amount of risk its stakeholders are willing to accept. Every risk gets evaluated against that threshold. Risks below the threshold are monitored, while risks above the threshold are treated.
Food fraud prevention needs to operate the same way. First, a company must identify its vulnerabilities, as well as their likelihood and potential impact. That information should be compared against the company's risk appetite. Then, the company should allocate resources to address the vulnerabilities that exceed its threshold.
This approach gives a defensible answer to "how much is enough." Instead of guessing or over-investing out of fear, companies can make rational, risk-based decisions using the same framework it applies to every other business risk. This also helps with prioritization. Every vulnerability cannot be addressed immediately, but the ones that matter most—i.e., those that exceed the risk appetite and pose the greatest threat—can be tackled first.
Education Opportunities
As supply chains become more digital and automated, many food fraud programs reflect older operating models. While most food safety professionals are well trained in hazard analysis and preventive controls, fewer have received formal training in food fraud vulnerability, food document fraud risk, or integration with enterprise risk management systems.
To help address the industry-wide capability gap, the Food Fraud Prevention Think Tank offers free, on-demand training through comprehensive MOOCs (Massive Open Online Courses) that cover vulnerability assessments, supply chain mapping, prevention strategies, and integration with enterprise risk management. These courses provide the foundational knowledge and practical tools needed to build or update a food fraud prevention program. Visit the Food Fraud Prevention Think Tank to access these resources and start building a prevention strategy today.
Building the Foundation for Fraud Prevention
The intersection of digitalization, omnichannel operations, and automation is creating both challenges and opportunities for food fraud prevention. The companies that will succeed are those that formalize their approach now, before the next crisis forces them to act.
Three things are needed to move forward:
- First, companies must update their food fraud vulnerability assessments to reflect their current supply chain realities, including digital document flows and automated systems.
- Second, food fraud prevention should be integrated with the formal Supply Chain Risk Management and Enterprise Risk Management systems so that organizations can work with their existing infrastructure rather than around it.
- Third, a risk-based framework should be used to answer the "how much is enough" question and allocate resources where they will have the greatest impact.
Supply chain management complexities are increasing, and the food fraud landscape is evolving. Enterprise systems need to evolve with it. That starts with recognizing that digitalization is not just about efficiency; it is about building resilient systems that can detect, prevent, and respond to fraud in an increasingly connected world.
Acknowledgment
Claude AI assisted with content synthesis and drafting under expert direction, with all conceptual frameworks, technical content, and editorial decisions determined by the authors.
References
- International Organization for Standardization (ISO). "ISO 22380:2018: Security and resilience—Authenticity, integrity and trust for products and documents—General principles for product fraud risk and countermeasures." Edition 1, 2018. https://www.iso.org/standard/73857.html.
- The 107th Congress. "H.R.3763—Sarbanes-Oxley Act of 2002." July 30, 2002. https://www.congress.gov/bill/107th-congress/house-bill/3763.
John W. Spink, Ph.D. is the Director and Lead Instructor for the Food Fraud Prevention Academy, as well as an Assistant Professor in the Department of Supply Chain Management in the College of Business at Michigan State University (MSU). His food fraud prevention research focuses on policy and strategy to understand and prevent supply chain disruptions and to implement procurement best practices. He is widely published in leading academic journals and has helped lead national and global regulatory and standards activity. More recently, his teaching and research has expanded to supply chain disruption management and procurement best practices.
Roy Fenoff, Ph.D. is an Associate Professor in the Department of Criminal Justice at The Military College of South Carolina (The Citadel). He is also a Forensic Handwriting and Document Examiner and an expert in forgery detection. Dr. Fenoff specializes in forgery and document fraud, food fraud and protection, and transnational crime.

